Please note instructions updated to include perfc.dat and perfc.dll files.
The advise on the files needed to prevent the encryption now included creating perfc.dat and perfc.dll files in the Windows directory in addition to the one without an extension.
Please note: this does not prevent the spread of NotPetya, at this time until the software is updated to prevent this from working, this just stops it encrypting your computer.
Following today’s(27th June 2017) manor cyber-attack outbreak for the NotPetya/GoldenEye bleepingcomputer have published an article on Vaccine, not Killswitch, Found for Petya (NotPetya) Ransomware Outbreak
They have supplied a bat script or instructions to apply this manually but if you want to apply it so the computers will receive it without a reboot you could use Group Policy Preferences.
- On a file share, the targeted computers have access to (e.g. read access by domain computers and domain controllers)
- Create a directory
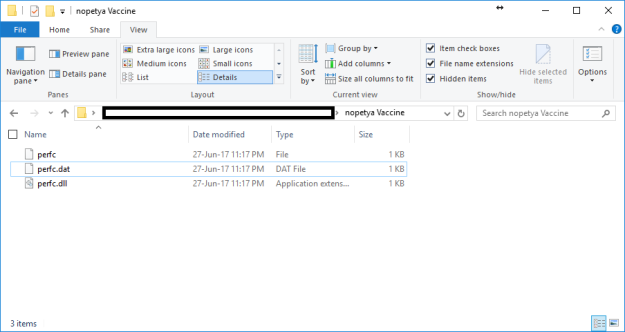
- Create a file named perfc (no file extension)
- Add some content to the file explaining what its for (example in the sctript linked above is “This is a NotPetya/Petya/Petna/SortaPetya Vaccination file. Do not remove as it protects you from being encrypted by Petya.”)
- Set the file to read only
- copy this file twice
- rename one to be perfc.dat
- rename the other to be perfc.dll
- Check all three files are readonly
- you should now have three files in that directory perfc, perfc.dat and perfc.dll
- Create a new group policy or edit an existing one targeted to all the computers you want to deploy the vaccine file to
- Edit the group policy
- Under Computer Configuration -> Preferences -> Windows Settings – Files
- Right click and select new -> file
- In the source file location enter the path to the directory you created earlier and append \*.* to the end of the path – e.g. \\server\share\nopetya Vaccine\*.*
- In the destination file enter c:\windows\
- Select Read-only
- Action should be create (note this will only create the files if they does not already exist in the destination) this is preferred as you would not want the files on the server if compromised to be copied again to the clients. Please note – any file in this directory will be copied to the c:\windows\ directory. If your not happy with this, you could create three ‘new -> file’ entries in the GPO, each explicitly naming the files you want to copy
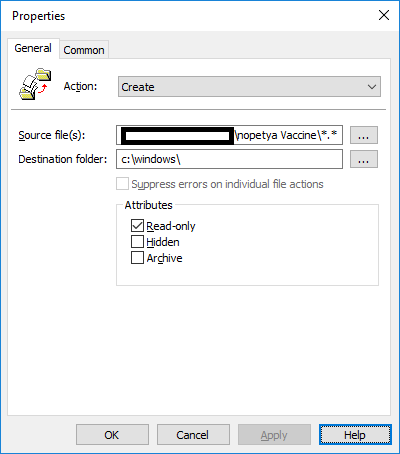
- Click OK
- run GPupdate /force on some computers to check
- the file “c:\Windows\perfc” is created and is read only
- the file “c:\Windows\perfc.dll” is created and is read only
- the file “c:\Windows\perfc.dat” is created and is read only
I accept no liability following this instructions of those found on third party websites I have linked to.

Do you not need to add the .dll and .dat file?
Thanks. The advise changed over night, I have now updated the post.
Pingback: Use Group Policy Preferences to deploy the NotPetya vaccine | Cybersecurity
Pingback: Petya: 5 regole per difenderti dal nuovo attacco malware - 4WARD
Pingback: After Wannacry, Now its Petya Ransomware hits worldwide - Yeah Hub
Thanks Edd
Have rolled this out to our machines, gives a little peace of mind for now at least!
Hello! Thanks for information.
I have a question:
When GP insert the files on some client computers, the files is read-only BUT can be changed. For example: I try rename the file, (logged on Admin user) and I got it. It is a problem?
Read only does not stop you renaming files, it only prevents the content of the file changing.
As I understand, NotPetya looks for the existence of the file and checks it is read only – If this is true it does not encrypt the computer. This does not stop it spreading though. I am not a security expert, I have read many articles about NotPetya and this way of deploying the files achieves the same thing and the scripts etc as the advise in those articles.
Thanks
Edd
I appreciate your response, thank you very much.
A hug from Brazil for you!
Thanks for your post.
As the files are set to read only this may cause issues with a new feature release (Windows 10) or and OS upgrade (say Windows 7 or 8.1 to 10) as the SYSTEM would need to be able to move the files to c:\windows.old\ (not 100% sure if the SYSTEM account can get around a read-only setting on the files for this but think that it can not) – could it be changed so that SYSTEM has full control if it can’t get around the read-only setting? Or has it been checked and verified that this will not cause issues in that case?
you can use local location for source, thus dropping need for share and increasing success rate
i.e source: %windir%\notepad.exe destination: %windir%\perfc
Thanks! Easy and powerfull. Great article.
Thank you. Really easy, well explained, and it worked!
Pingback: Petna/Petya vaccine e killswitch | Luca Donetti Dontin